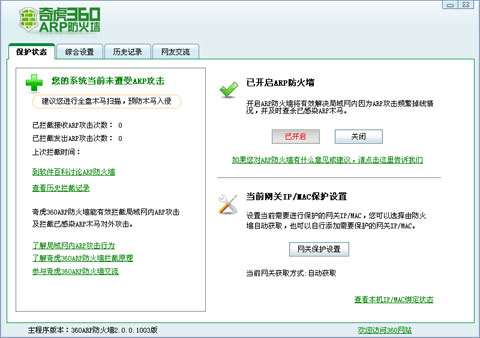
首先需要进行linux的基础安全设置,可以先参考这篇文章
http://www.zzvips.com/article/204472.html
1、Linux系统脚本
|
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
82
83
84
85
86
87
88
89
90
91
92
93
94
95
96
97
98
99
100
101
102
103
104
105
106
107
108
109
110
111
112
113
114
115
116
117
118
119
120
121
122
123
124
125
126
127
128
129
130
131
132
133
134
135
136
137
138
139
140
141
142
143
144
145
146
147
148
149
150
151
152
153
154
155
156
157
158
159
160
161
162
163
164
165
166
167
168
169
170
171
172
173
174
175
176
177
178
179
180
181
182
183
184
185
186
187
188
189
190
191
192
193
194
195
196
197
|
#!/bin/bash##########################################Function: linux drop port#Usage: bash linux_drop_port.sh#Author: Customer Service Department#Company: Alibaba Cloud Computing#Version: 2.0######################################### check_os_release(){ while true do os_release=$(grep "Red Hat Enterprise Linux Server release"/etc/issue 2>/dev/null) os_release_2=$(grep "Red Hat Enterprise Linux Server release"/etc/redhat-release 2>/dev/null) if [ "$os_release" ] && [ "$os_release_2" ] then if echo "$os_release"|grep "release 5" >/dev/null2>&1 then os_release=redhat5 echo "$os_release" elif echo "$os_release"|grep "release 6">/dev/null 2>&1 then os_release=redhat6 echo "$os_release" else os_release="" echo "$os_release" fi break fi os_release=$(grep "Aliyun Linux release" /etc/issue2>/dev/null) os_release_2=$(grep "Aliyun Linux release" /etc/aliyun-release2>/dev/null) if [ "$os_release" ] && [ "$os_release_2" ] then if echo "$os_release"|grep "release 5" >/dev/null2>&1 then os_release=aliyun5 echo "$os_release" elif echo "$os_release"|grep "release 6">/dev/null 2>&1 then os_release=aliyun6 echo "$os_release" else os_release="" echo "$os_release" fi break fi os_release=$(grep "CentOS release" /etc/issue 2>/dev/null) os_release_2=$(grep "CentOS release" /etc/*release2>/dev/null) if [ "$os_release" ] && [ "$os_release_2" ] then if echo "$os_release"|grep "release 5" >/dev/null2>&1 then os_release=centos5 echo "$os_release" elif echo "$os_release"|grep "release 6">/dev/null 2>&1 then os_release=centos6 echo "$os_release" else os_release="" echo "$os_release" fi break fi os_release=$(grep -i "ubuntu" /etc/issue 2>/dev/null) os_release_2=$(grep -i "ubuntu" /etc/lsb-release2>/dev/null) if [ "$os_release" ] && [ "$os_release_2" ] then if echo "$os_release"|grep "Ubuntu 10" >/dev/null2>&1 then os_release=ubuntu10 echo "$os_release" elif echo "$os_release"|grep "Ubuntu 12.04">/dev/null 2>&1 then os_release=ubuntu1204 echo "$os_release" elif echo "$os_release"|grep "Ubuntu 12.10">/dev/null 2>&1 then os_release=ubuntu1210 echo "$os_release" else os_release="" echo "$os_release" fi break fi os_release=$(grep -i "debian" /etc/issue 2>/dev/null) os_release_2=$(grep -i "debian" /proc/version 2>/dev/null) if [ "$os_release" ] && [ "$os_release_2" ] then if echo "$os_release"|grep "Linux 6" >/dev/null2>&1 then os_release=debian6 echo "$os_release" else os_release="" echo "$os_release" fi break fi os_release=$(grep "openSUSE" /etc/issue 2>/dev/null) os_release_2=$(grep "openSUSE" /etc/*release 2>/dev/null) if [ "$os_release" ] && [ "$os_release_2" ] then if echo "$os_release"|grep"13.1" >/dev/null 2>&1 then os_release=opensuse131 echo "$os_release" else os_release="" echo "$os_release" fi break fi break done} exit_script(){ echo -e "\033[1;40;31mInstall $1 error,will exit.\n\033[0m" rm-f $LOCKfile exit 1} config_iptables(){ iptables -I OUTPUT 1 -p tcp -m multiport --dport21,22,23,25,53,80,135,139,443,445 -j DROP iptables -I OUTPUT 2 -p tcp -m multiport --dport 1433,1314,1521,2222,3306,3433,3389,4899,8080,18186-j DROP iptables -I OUTPUT 3 -p udp -j DROP iptables -nvL} ubuntu_config_ufw(){ ufwdeny out proto tcp to any port 21,22,23,25,53,80,135,139,443,445 ufwdeny out proto tcp to any port 1433,1314,1521,2222,3306,3433,3389,4899,8080,18186 ufwdeny out proto udp to any ufwstatus} ####################Start####################check lock file ,one time only let thescript run one timeLOCKfile=/tmp/.$(basename $0)if [ -f "$LOCKfile" ]then echo -e "\033[1;40;31mThe script is already exist,please next timeto run this script.\n\033[0m" exitelse echo -e "\033[40;32mStep 1.No lock file,begin to create lock fileand continue.\n\033[40;37m" touch $LOCKfilefi #check userif [ $(id -u) != "0" ]then echo -e "\033[1;40;31mError: You must be root to run this script,please use root to execute this script.\n\033[0m" rm-f $LOCKfile exit 1fi echo -e "\033[40;32mStep 2.Begen tocheck the OS issue.\n\033[40;37m"os_release=$(check_os_release)if [ "X$os_release" =="X" ]then echo -e "\033[1;40;31mThe OS does not identify,So this script isnot executede.\n\033[0m" rm-f $LOCKfile exit 0else echo -e "\033[40;32mThis OS is $os_release.\n\033[40;37m"fi echo -e "\033[40;32mStep 3.Begen toconfig firewall.\n\033[40;37m"case "$os_release" inredhat5|centos5|redhat6|centos6|aliyun5|aliyun6) service iptables start config_iptables ;;debian6) config_iptables ;;ubuntu10|ubuntu1204|ubuntu1210) ufwenable <<EOFyEOF ubuntu_config_ufw ;;opensuse131) config_iptables ;;esac echo -e "\033[40;32mConfig firewallsuccess,this script now exit!\n\033[40;37m"rm -f $LOCKfile |
上述文件下载到机器内部直接执行即可。
2、设置iptables,限制访问
|
1
2
3
4
5
6
7
8
9
10
11
12
13
|
/sbin/iptables -P INPUT ACCEPT/sbin/iptables -F/sbin/iptables -X/sbin/iptables -Z/sbin/iptables -A INPUT -i lo -j ACCEPT /sbin/iptables -A INPUT -p tcp --dport 22 -j ACCEPT/sbin/iptables -A INPUT -p tcp --dport 80 -j ACCEPT/sbin/iptables -A INPUT -p tcp --dport 8080 -j ACCEPT/sbin/iptables -A INPUT -p icmp -m icmp --icmp-type 8 -j ACCEPT/sbin/iptables -A INPUT -m state --state ESTABLISHED -j ACCEPT/sbin/iptables -P INPUT DROP service iptables save |
以上脚本,在每次重装完系统后执行一次即可,其配置会保存至/etc/sysconfig/iptables
更详细的可以参考这篇文章 http://www.zzvips.com/article/204471.html
3、常用网络监控命令
(1) netstat -tunl:查看所有正在监听的端口
|
1
2
3
4
5
6
7
8
|
[root@AY1407041017110375bbZ ~]# netstat -tunlActive Internet connections (only servers)Proto Recv-Q Send-Q Local Address Foreign Address State tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN udp 0 0 ip:123 0.0.0.0:* udp 0 0 ip:123 0.0.0.0:* udp 0 0 127.0.0.1:123 0.0.0.0:* udp 0 0 0.0.0.0:123 0.0.0.0:* |
其中123端口用于NTP服务。
(2)netstat -tunp:查看所有已连接的网络连接状态,并显示其PID及程序名称。
|
1
2
3
4
5
|
[root@AY1407041017110375bbZ ~]# netstat -tunpActive Internet connections (w/o servers)Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name tcp 0 96 ip:22 221.176.33.126:52699 ESTABLISHED 926/sshd tcp 0 0 ip:34385 42.156.166.25:80 ESTABLISHED 1003/aegis_cli |
根据上述结果,可以根据需要kill掉相应进程。
如:
kill -9 1003
(3)netstat -tunlp
(4)netstat常用选项说明:
-t: tcp
-u : udp
-l, --listening
Show only listening sockets. (These are omitted by default.)
-p, --program
Show the PID and name of the program to which each socket belongs.
--numeric , -n
Show numerical addresses instead of trying to determine symbolic host, port or user names.
4、修改ssh的监听端口
(1)修改 /etc/ssh/sshd_config
原有的port 22
改为port 44
(2)重启服务
/etc/init.d/sshd restart
(3)查看情况
|
1
2
3
4
5
6
7
8
|
netstat -tunlActive Internet connections (only servers)Proto Recv-Q Send-Q Local Address Foreign Address State tcp 0 0 0.0.0.0:44 0.0.0.0:* LISTEN udp 0 0 ip:123 0.0.0.0:* udp 0 0 ip:123 0.0.0.0:* udp 0 0 127.0.0.1:123 0.0.0.0:* udp 0 0 0.0.0.0:123 0.0.0.0:* |